I spend a couple of minutes every day going through GitHub repos related to security tools to see if I find a new tool that might be of interest to me, today that tool is Microsoft's Attack Surface Analyzer.
Attack Surface Analyzer (ASA) is a Microsoft-developed Security tool that analyzes the attack surface of a Windows, Linux or MacOS system and reports on system changes that may have potential security implications that are introduced by the installation of software or by system misconfiguration.
Installation
You can install ASA in a couple of different ways, either through the CLI (command below, requires .NET Core installed) or by downloading the binaries from the GitHub repository.
dotnet tool install -g Microsoft.CST.AttackSurfaceAnalyzer.CLITesting It Out
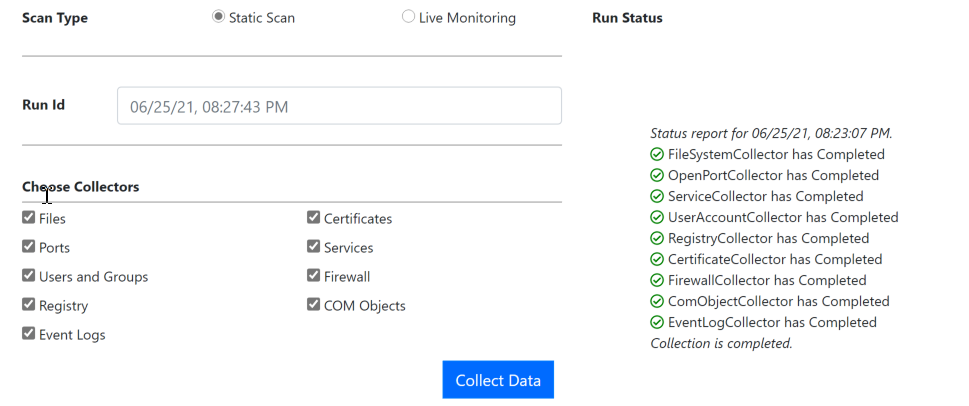
I spun up a Windows VM on my laptop, installed .Net, installed ASA, and ran the GUI to do the baseline scan (you need to do this one on a clean machine).
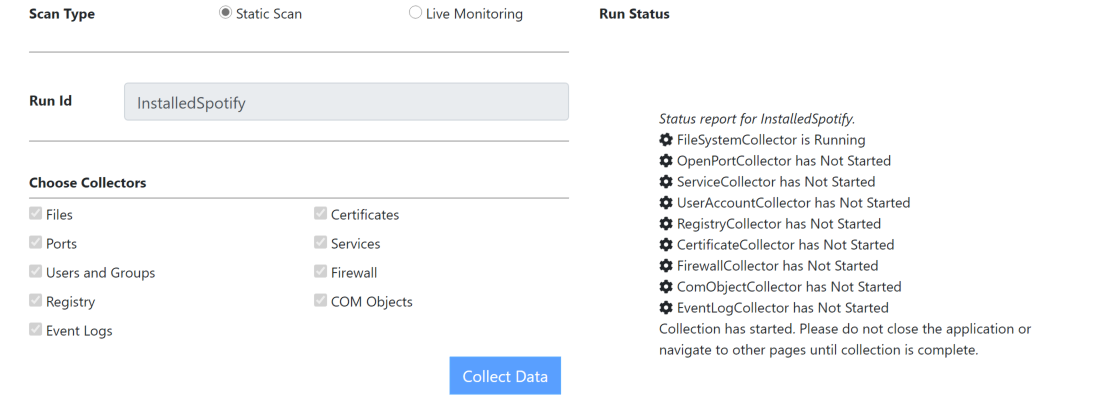
Once you have your baseline, you can install the application you want to analyse, in my case I installed Spotify, once the installation is complete, I ran the ASA scan again to detect changes to the system.
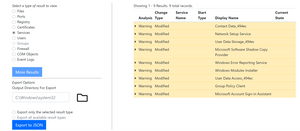
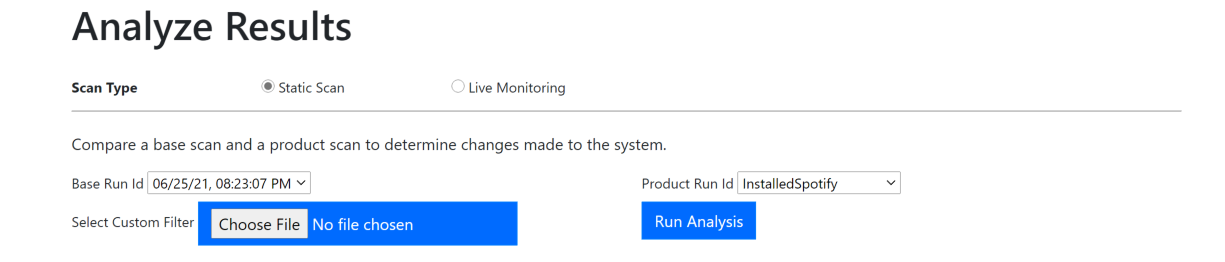
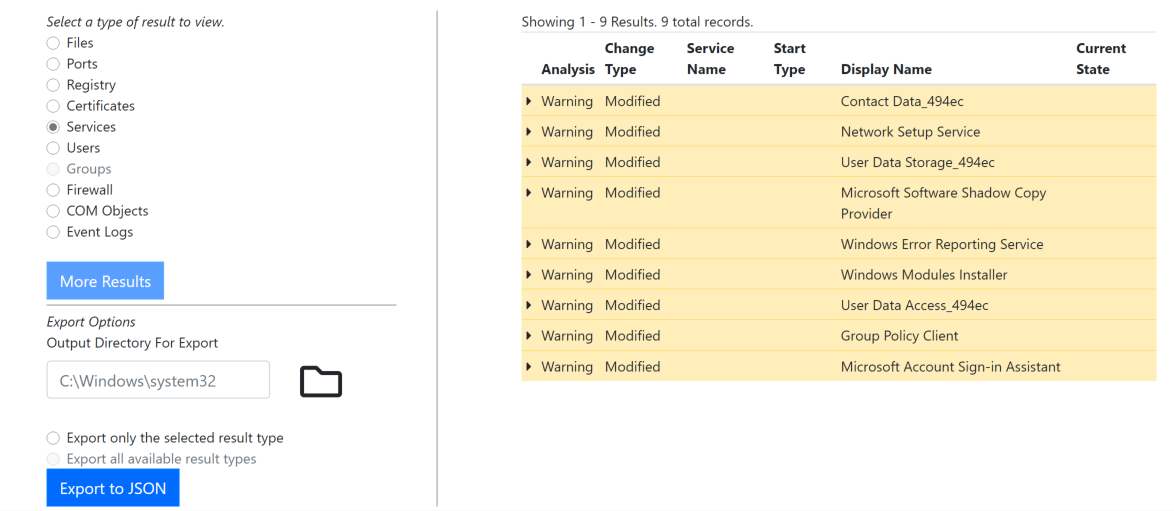
Once both scans are done, you can analyse the results by comparing the results from both scans to see what happened on the system after installing Spotify.
You can choose which type of changes you are interested in (e.g. Files, Ports, Users, ...) and see if your installed application did any changes. Granted, I ran the analysis directly after installing the application, the results will vary depending on when the data collection is performed (more changes might happen as you use the application).
First Thoughts
ASA runs pretty smoothly and is super easy to use. It can be a true asset for people trying to understand the inner workings of applications and/or tools before introducing them into production environments. I only explore a simple scenario, the possibilities are wide open, give it a try.
Links
- microsoft/AttackSurfaceAnalyzer: Attack Surface Analyzer can help you analyze your operating system's security configuration for changes during software installation. (github.com)
- Download Attack Surface Analyzer 2.0 from Official Microsoft Download Center
- Home · microsoft/AttackSurfaceAnalyzer Wiki (github.com)