Google Workspace is one of the most popular productivity suites available on the market at the moment with hundreds of millions of users and a rather decent set of services covering a wide range of daily activities (document editing, presentations, meetings, ...).
I used Google services a lot and even administrated a Google Workspace tenant for a student organization at one point in my life, but I never got to see and experiment with the tools Google makes available to Enterprise customers, one of which is the topic of this blog post, the security investigation tool.
If you are a security administrator who works with Google services or aids other administrators who do, this tool is indispensable. It allows you to review logs for many of the Google services (e.g. Gmail, Drive, Meet, ...) and take actions to remedy security or privacy concerns (e.g. delete malicious messages, detect unauthorized documents access, and many more).
The security investigation tool is a resource in the Google Workspace security center that can help you identify, triage, and take action on security and privacy issues in your domain. (Soruce)
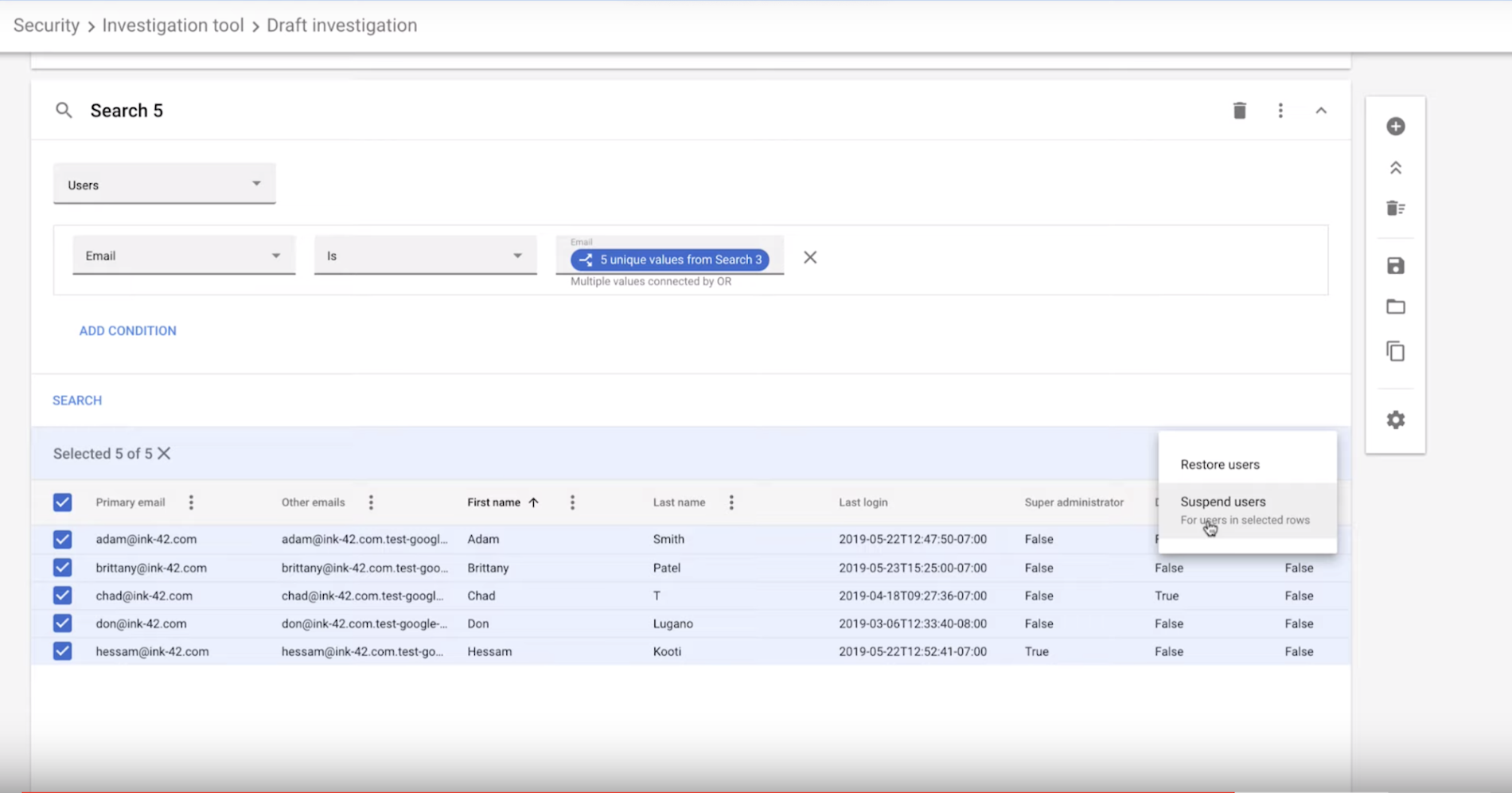
Sam Lugani, the Head of Security for GCP Platform & Google Workspace, published a blog post back in 2019 detailing how the various features of the investigation tools can be used to detect and respond to attacks. I highly recommend reading that blog post and watching the YouTube video, they are very informative.
It's quite a pity this wonderful tool is only available for Enterprise users, but if you manage to get your hands on it as part of your daily work, I highly recommend make the best use of it to strength your Google Workspace security and privacy tooling.
Links
- https://cloud.google.com/blog/products/g-suite/admin-insider-these-6-steps-can-help-you-block-security-threats-in-g-suite
- https://workspaceupdates.googleblog.com/2020/12/security-center-investigation-tool-logs-google-chat-meet-groups-calendar-voice.html
- About the security investigation tool (https://support.google.com/a/answer/7575955)
- Customize searches within the investigation tool (https://support.google.com/a/answer/7587832)
- Admin auditing for the security center (https://support.google.com/a/answer/7632917)
Cover image from Link

