I am in Luxembourg for a few days attending three different information security events that are part of the LuxSecurityWeek which is held every October. This is my second time attending these events and it’s becoming more of a personal habit for many reasons. Luxembourg is a beautiful country, very safe, and close to many European traveling hubs.
As I mentioned, this is my second time attending Hack.lu, I came here last year, and I will come again next year. The conference is great in every aspect (content, speakers, atmosphere, food, … ). Sometimes my anxiety gets the best of me but most of the time I enjoy the overall experience and I get to talk to many people, exchange knowledge with them, and even make some network connections for future professional networking. A massive kudos to the organizers who created such a nice informative event.
Credit: All videos are recorded and uploaded by the amazing @cooper. You can find the full list on his website: https://administraitor.video/edition/Hack.lu/2019
Without further ado, let’s recap the awesome talks from Hack.lu first day, I hope you enjoy this quick summary.
Smartphone apps: let’s talk about privacy
The day started with an easy to follow yet highly informative talk from Axelle Apvrille (@cryptax) who walked us through some great research she’s done in the field of mobile phone apps privacy. She selected 20 applications at random and performed an analysis to determine how they perform in various aspects of privacy (What permissions they ask for, what are they doing locally, …).
The results were (as you might have expected) shocking. From cooking apps that require your location to apps that are full of SDKs and tracking code. The talk was a good reminder that many of the popular apps we use on a daily basis are terrible when it comes to privacy. I noted down some tools and checks that I would personally like to perform on any app before installing it on my phones.
Fingerpointing False Positives
The second talk was “Fingerprinting False Positives: How to better integrate Continuous Improvement into Security Monitoring” presented by Desiree Sacher (@d3sre). She presented a taxonomy she’s created to assist SoC analysts to refocus their attention when they are faced with loads of false positives. Her research really hit a nerve and while I can’t for all the attendees, I definitely understand and relate to many of the challenges she addressed in her taxonomy. Make sure to check her GitHub account for more details on how to use the taxonomy in a real-life use case.
Tiplines Today
Next was the Tiplines Today talk by Harlo Holmes (@harlo) who talked about her work with the Freedom of the Press Foundation and how they help journalists and sources maintain their privacy and safety in an ever-changing world packed with legal troubles and unreasonable expectations. She gave a great overview of current systems and mediums that are used for secure contact between journalists and their sources. She also highlighted many of the common pitfalls of these systems and how they can expose their users to serious risks and harm. The talk was packed with information, insights and thought-provoking questions. When it was over, I realized I need to Google a lot of terms to improve my understanding of the topic.
The Road to Hell is Paved with Bad Passwords
This talk was so crazy it felt like reading the plot of a Hollywood movie and of course, a super bad password (123456) was at the center of the talk. Titled “The road to hell is paved with bad passwords”, the talk was presented by Chris Kubecka (@SecEvangelism). In case you don’t know Chris, here is her Wikipedia page which sheds some light on her career and track record which is super impressive, to say the least. I don\t want to spoil the talk for you but I can tell you it includes drones, surveillance, threats, state actors, insiders, embassies and lots of highly stressful situations. A great story and informative talk.
Say Cheese – How I Ransomwared your DSLR Camera
I remember Eyal (@EyalItkin) from his talk during the last edition of Hack.lu in which he demonstrated a novel method of hacking printers. He is back and he has more amazing research to share with the community, this time it’s hacking your cameras. Eyal presentations are a work of art in which he takes the audience through the entire process of his research from the initial idea to the final PoC development and demo. It’s always fascinating to attend one of his presentations because I can guarantee you will learn a lot about the topic he is talking about. In this talk, he managed to find vulnerabilities in the firmware of a Canon camera and he then used these vulnerabilities to build ransomware that can be used to encrypt the pictures on the memory card.
The Regulation (EU) 2019/796 Of 17 May 2019 Concerning Restrictive Measures Against Cyber-attacks Threatening The Union Or Its Member States
This talk had a long title but we can blame that on the name of the regulation being addressed. Presented by Eve Matringe, the talk gives a quick overview of the regulation and how it can affect countries’ response to cyber-attacks targeting member states of the union. Eve also discussed some of the vague aspects that might be open to interpretation and abuse by European countries which might result in unfair situations where someone is blacklisted on false grounds but has no path for recourse. It was an interesting talk and it prompted me to look up the regulation and add it to my reading list. Sadly, I don’t think this talk was recorded.
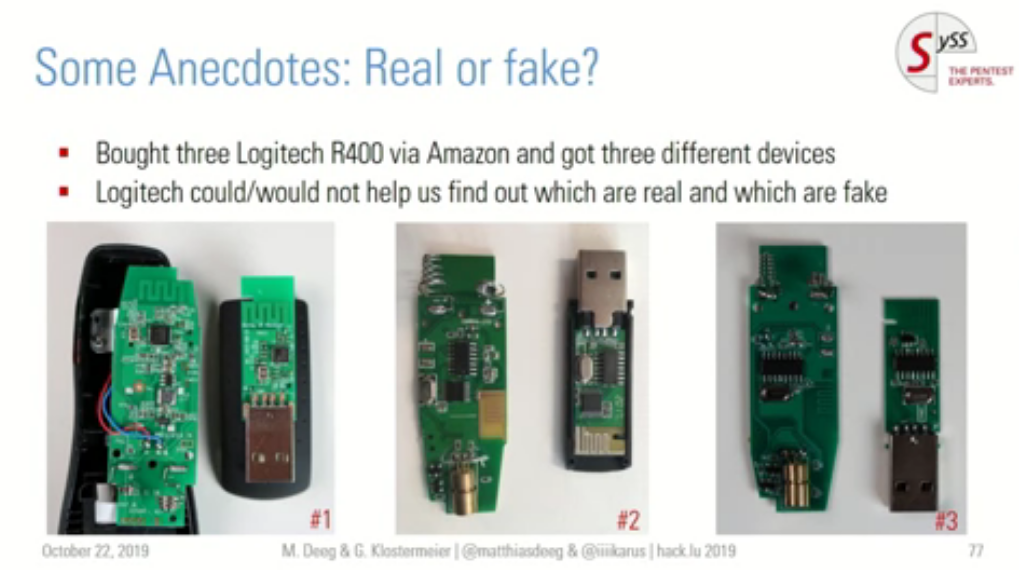
New Tales of Wireless Input Devices
In his talk, Gerhard Klostermeier told interesting tales of security vulnerabilities in wireless input devices and the results from their (him and Matthias Deeg) research into this topic. Needless to say, I am considering the possibility of throwing away my wireless input devices and going back to old school wired devices. The following slide made me super worried:
Memory forensics analysis of Cisco IOS XR 32 bits routers with ‘Amnesic-Sherpa’
In his talk, Solal Jacob gave some background information about operating systems used in routers and some more specific information about the Cisco IOS XR-32 before moving to introduce and explain the details of the memory acquisition tool they developed for this specific use case.
Kill MD5 – demystifying hash collisions
I missed this talk so I will watch the video recording and I recommend you do the same.
Last Words
Overall, the day was great and I really enjoyed the content that was presented throughout the day. There were workshops but I opted for attending talks during this first day and marked few workshops of interest that I will attend in the upcoming day. I am looking forward to the second day. It’s late and I am tired so I will leave here and will write another recap post tomorrow. Hope you enjoyed reading this quick recap.
Copyrights are reserved for their respective owners.
